Best Practices To Prevent Account Takeover
by Arnab Dey Business Intelligence Published on: 10 August 2022 Last Updated on: 20 September 2023

A common problem that small businesses face is account takeover. In this article, we will provide you with the best practices for preventing account takeover.
Whether this be shoulder surfing and simply observing someone’s account information in order to gain access or sophisticated ato attacks which utilize social engineering or decoy links. There is always a fraud case at hand in which a malicious third-party user seeks to cause damage or gain from the misuse of another individual or organisation’s data or account access.
Account takeover protection is a term used to describe various security measures that a business can take in order to protect its online accounts from being accessed by unauthorized individuals.
7 Best Practices For Preventing The Account Takeover
Here are a few best practices that you can implement to protect your business from account takeover fraud chances.
1. Use Strong Passwords:
Passwords are one of the most important measures that you can take to protect your online accounts from being accessed by unauthorized individuals. Make sure that your passwords are at least eight characters long and include a mix of upper and lowercase letters, numbers, and symbols.

Do not use easily guessable passwords or those that are easily accessible on the internet. The account takeover vulnerability is always there. So always give the maximum preferences for creating strong passwords. For hackers, every password breaking is possible. But a strong password is a stronger step.
2. Use Two-Factor Authentication:
Two-factor authentication requires users to provide not only their username and password but also a unique code generated by the provider (such as a text message). This type of authentication is often more secure than standard username and password authentication because it increases the chances that the user will be able to log in if their login credentials are compromised.
The two-phase authentication process makes your work easy. And it holds a stronger and more secure position. If you like to build up a secure authentication process, then do not skip the two-step authentication process. It will protect your account from account takeover chances.
3. Keep Your Computer Security Up To Date:
Keeping your computer security up to date is one of the best practices to prevent account takeover. Doing this will ensure that someone cannot take over your account without your knowledge.

Make sure to install updated antivirus software, keep your operating system and applications up-to-date, and use strong passwords. Additionally, make sure to regularly back up your computer files in case something happens to your hard drive and you need to restore them.
4. Be Aware Of Phishing Schemes:
Phishing schemes are fraudulent emails and account takeover chances that look like they come from legitimate businesses (such as your bank or email provider).
The goal of these schemes is usually to trick you into revealing sensitive information (such as your account login credentials) by compromising the trust that you have in these institutions.
Be cautious about clicking on any links in unsolicited emails, even if they seem trustworthy. If in doubt, contact the company directly for clarification about the email content or sender.
5. Do Not Give Out Personal Information:
One of the surefire ways to prevent your account from being taken over is to keep your personal information as confidential as possible.

This means never sharing your username or password with anyone and avoiding any unsolicited requests for personal information.
Additionally, always use strong passwords that are at least eight characters long and include a combination of letters, numbers, and symbols.
6. Baseline Typical Account Behaviour:
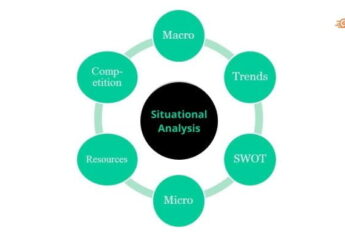
A business should baseline typical account behavior in order to prevent account takeover. This includes observing user activity, tracking the number of interactions, and understanding customer requirements.
Additionally, a business can use security measures such as two-factor authentication and secure passwords to help protect their accounts from potential threats.
7. Pinpointing The Attackers:
There are several ways to identify attackers, but the most important thing is to determine if they are insiders or outsiders. Outsiders typically use publicly available tools, while insiders use tools that are specific to their organization.

For example, insiders might use a company’s internal email system to launch an attack, while outsiders might use the company’s public internet address. Once you’ve determined who is attacking your account, you need to take steps to prevent them from taking over your account.
The most important step is to create strong passwords and keep them private. You can also protect your account by enabling two-factor authentication and setting up a security code.
Final Thoughts:
A few best practices can be used to prevent account takeover. First, ensure that your usernames and passwords are strong and unique. Also, do not allow users to create new accounts easily, and ensure that you have a firm password policy.
Finally, always monitor your account for suspicious activity and take appropriate action if necessary. If you follow these best practices, you’ll be more likely to prevent an account takeover from occurring and keep your confidential information safe. By following these simple steps, you can protect your business from being taken over by a cyber attacker.
Read Also: